Review: Steve Jackson's Hacker
Review by The Devil's Advocate
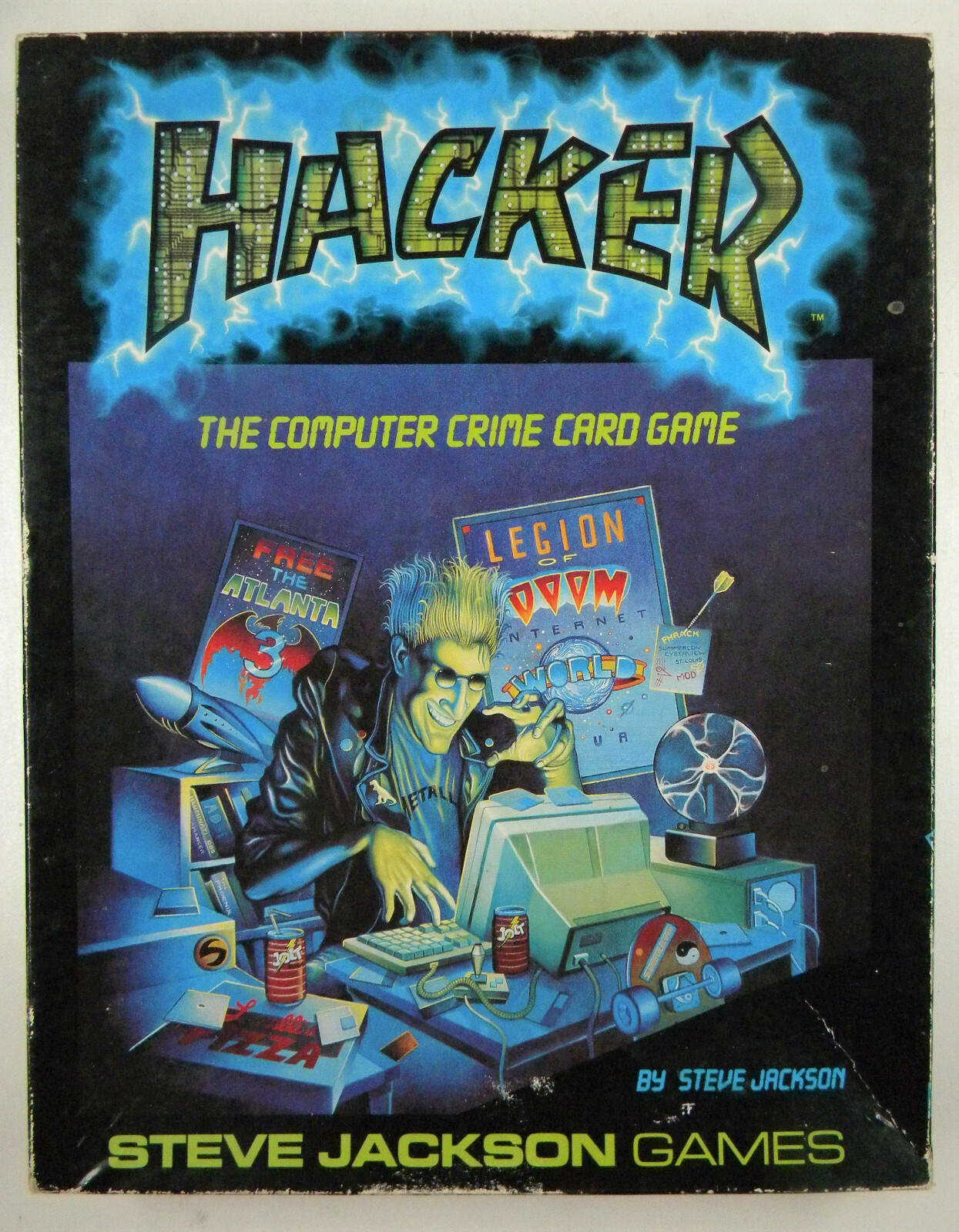
Hacker: The Computer Crime Card Game by Steve Jackson $19.95, Steve Jackson Games |
I watched with envy as Emmanuel Goldstein gained access to NORAD. He had used a hidden in-dial together with a password file, and was now on the MILNET. I looked around the table to see what the other hackers would do. Nothing. They were all just a bunch of Amiga-lamers anyway. If anyone was going to stop Emmanuel, it would have to be me, the Net Ninja. I kept a close eye on him as he hopped over to The Pentagon on the MILNET. Riding on nothing but caffeine and pizza, he was hacking like a crazed Dutchman. He was trying to brute-hack his way in, using every trick he had. He needed those tricks, too, because the ice on that system was numbin'. But I had a few tricks of my own. I watched and waited while Emmanuel penetrated one of the most powerful systems on the net. Then I raided the bastard...
Hacker: The Computer Crime Card Game, is Steve Jackson's latest gaming foray into the hacking/phreaking world. As the introduction explains, the game was conceived after the Secret Service wrongfully raided his company in 1990. Jackson's response was a logical one: sue the Secret Service and make a game about it. Hacker, then, is Jackson's way of letting the Secret Service know how much he appreciated having his rights violated.
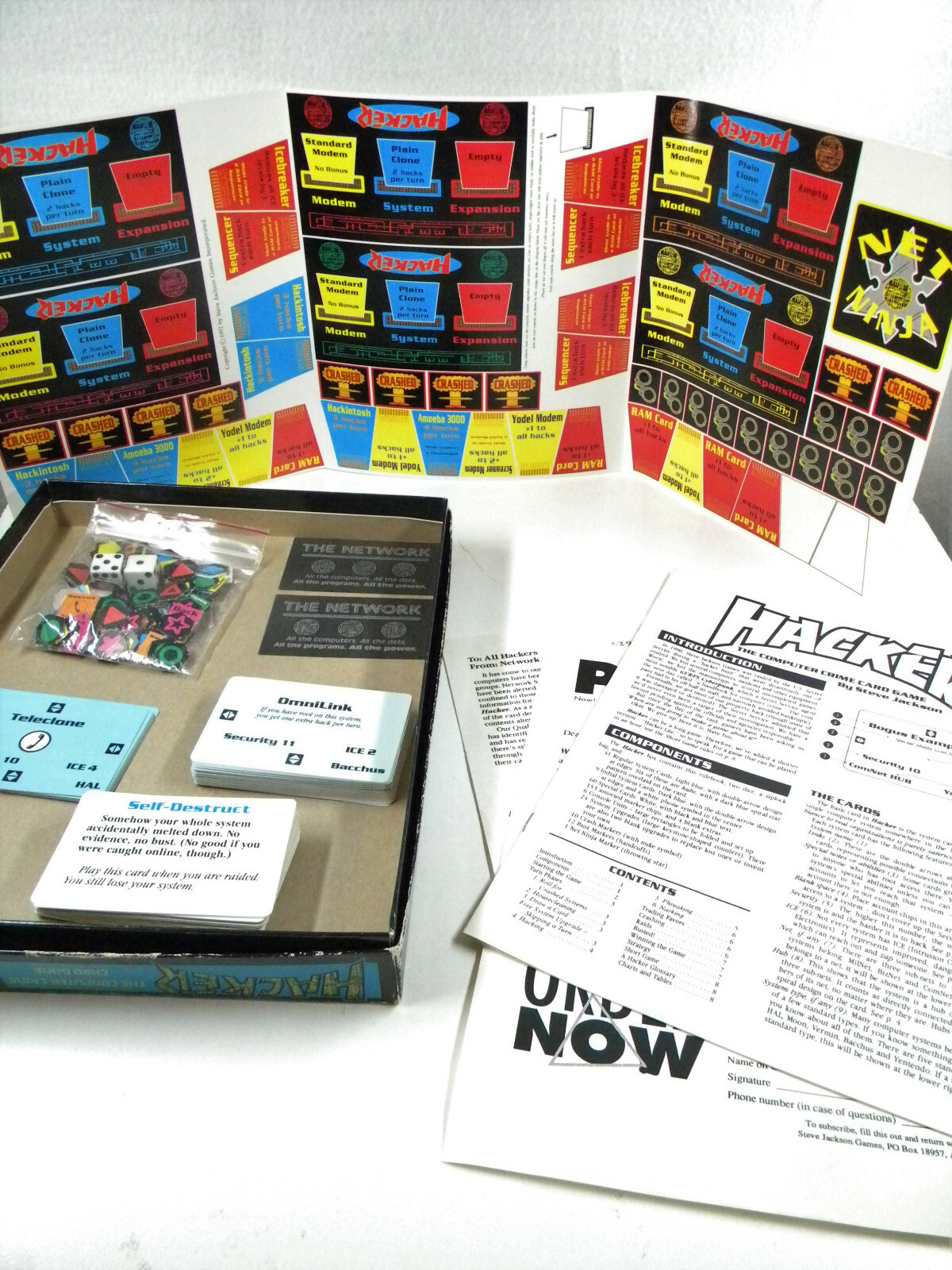
Hacker has all the elements of its namesake: players can hack, phreak, upgrade their computer equipment, crash systems, use secret in-dials, use back doors, travel on various networks, trade or coerce favors, nark on friends, raid or get raided (and possibly busted). The goal of the game is to be the first hacker to gain twelve or more active accounts. This number will vary depending on how long you wish to play. With five or six players, a typical game can last all night.
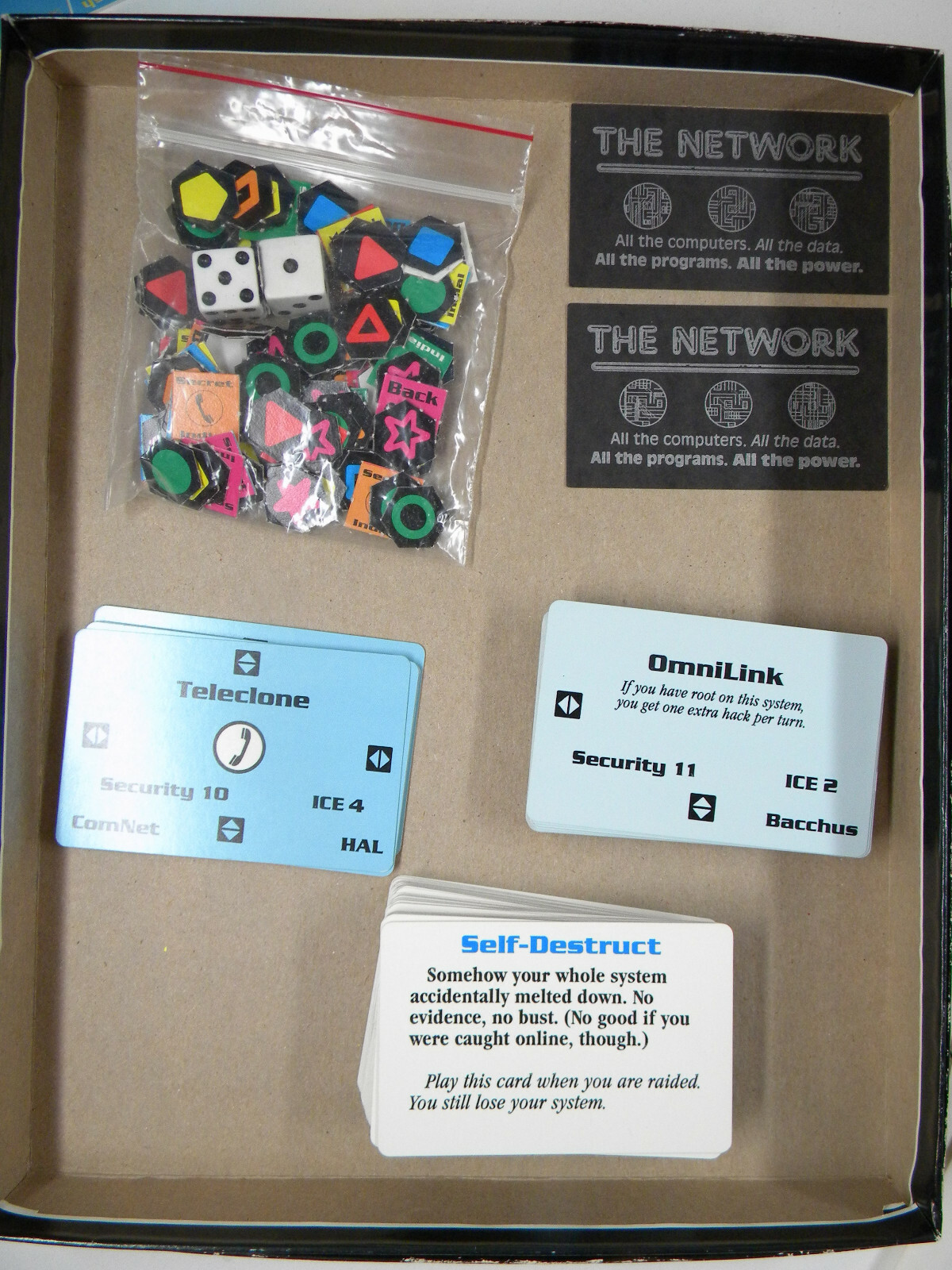
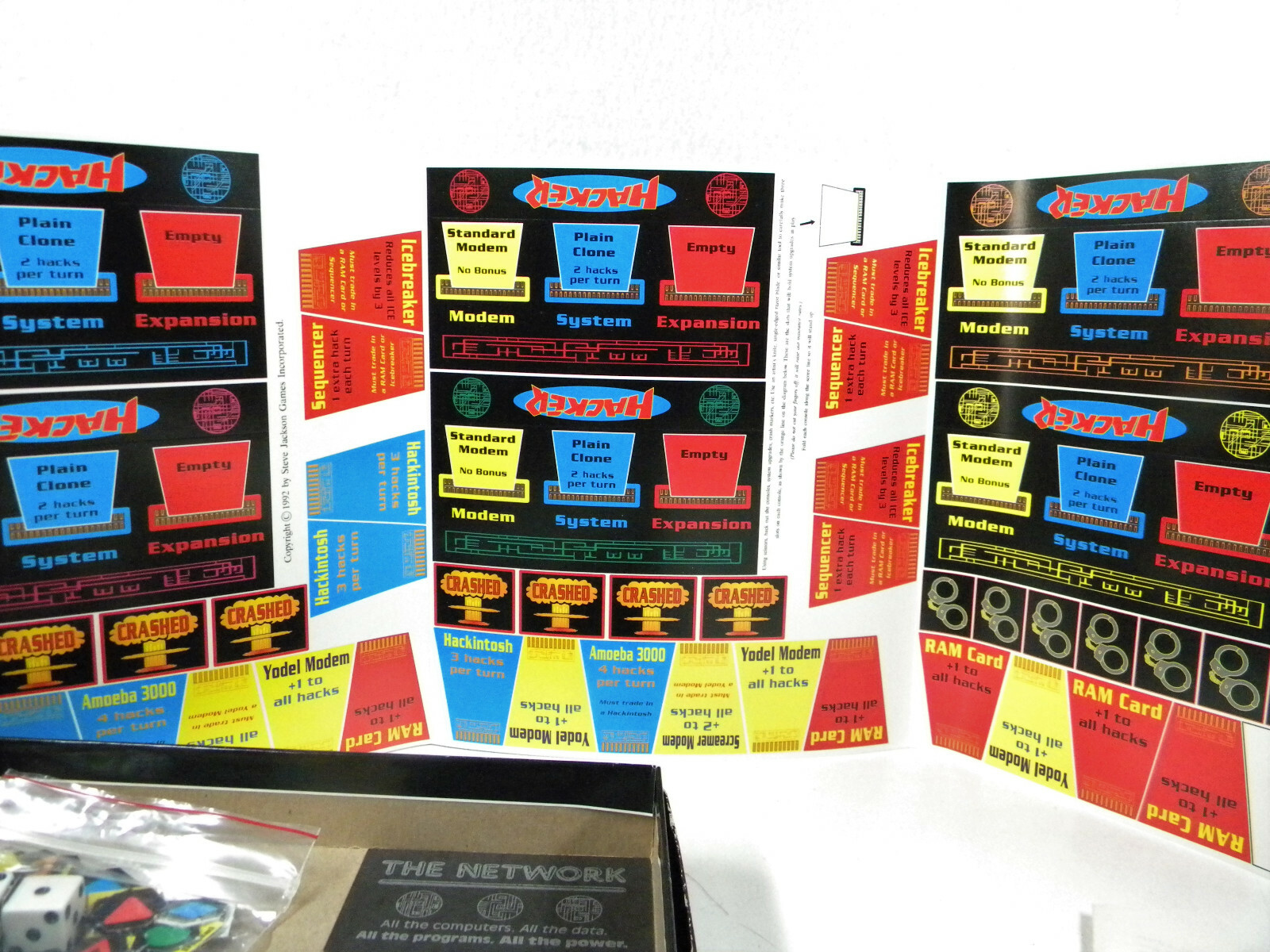
Those who are familiar with Illuminati will have no problem adapting to the look and feel of the game. The action takes place on an array of cards that, together, comprise the computer network. Each card represents an individual computer system complete with its own security and ICE levels, as well as networking information. Before the game begins, these "System" cards are dealt randomly to the players, who then proceed to "link" the cards together by laying them down on a flat surface next to each other. Players may arrange the cards in any way they see fit, although some rules exist to regulate this initial setting-up process. Some cards will only link in one direction, while other cards are multi-linkable.
Throughout the game, the playing area or "net" expands as more System cards are added. The advantage to using this Iluminati-style "board" is that no two games are ever the same; the playing area is always changing. The only disadvantage to this is that the game will require a large, flat playing surface, so playing on a Ferris wheel is out of the question.
A typical turn begins by drawing a random "special" card. These cards are always beneficial to the player who draws them. They can be offensive, defensive, or just plain helpful. The Secret Service Raid card, for example, is played on an opponent: "Lose all your equipment. Roll 7 or better to avoid a bust. Play on a rival after any successful hack by any player..."
Some cards counteract the effects of other cards. The Dummy Equipment card, for instance, might be used after a raid: "The investigators took your TV and your old Banana II, but they overlooked the real stuff. No evidence, no bust - and you keep your system..."
Other cards will give you much needed bonuses such as extra hacks or additions to your dice rolls. The Caffeine and Pizza card, "Perfect for that manic burst of energy," will give you one extra hack, while the Social Engineering or Trashing card gives bonuses to your dice rolls. In addition, some cards are used only once, while others can be reused. All in all, the special cards are a nice touch and add character to the game.
After taking a special card, a player must answer that self-incriminating question: To hack or not to hack? Why would anyone not want to hack in a game called Hacker? The answer is that a player may choose not to hack so that he or she can upgrade instead. Like certain special cards, upgrades will give players bonuses such as extra hacks or additions to dice rolls. A player who opts to upgrade ends his or her turn without much excitement.
Hacking is naturally the main course of the game. Skill is required in choosing the right system and in finagling the bonuses necessary in order to beat the system's security level. A player must begin by hacking one of the in-dials, which are entrances to the various other systems on the net. In order to get an account on a system, a player must tie or beat the system's security level. If a player manages to get four points higher than the security level, then this is indicative of good hacking and a root account is obtained. Root accounts allow extra privileges and bonuses under certain circumstances. For instance, root can initiate a housecleaning to rid a system of other unwanted hackers.
When hacking, a player must also avoid any ICE that may be present on the system. ICE, short for, Intrusion Countermeasure Electronics, obviously doesn't exist yet, but Jackson couldn't resist the Gibsonian concept which is so ingrained in hackers that it might as well exist anyway. Avoiding ICE is a matter of rolling higher than a system's ICE level. A player who is ICE'd will experience discomfort as he or she loses accounts on various systems. In some cases, hitting ICE also results in a raid.
Each system has its own security level. Most systems also have ICE, and some even offer special privileges for those who have root access. No Such Agency, for instance, allows players with root accounts to draw an extra special card at the end of their turn. Naturally, the better a system is, the higher its security and ICE levels.
The next phase of a player's turn is phreaking. This option allows fellow hackers a chance to gain access to a system that is already compromised by the player. Phreaking is a good faith option, designed to allow players to work together toward their mutual goal of system conquest. However, phreaking also has its risks, as it is still possible to hit ICE. Phreaking also fills up systems with hackers. The disadvantage to having too many hackers on a system is that it automatically initiates housecleaning. At the start of a player's turn, he or she must "roll for housecleaning" on all systems where four or more hackers are present. Housecleaning is the real-life equivalent of a system administrator doing his or her job. Housecleaning forces each hacker to roll well or be tossed off the system. Naturally, players with root accounts have better chances. Phreaking, then, can be both beneficial and baneful.
The final phase of a player's turn is narking. Turning your fellow hackers in may seem like the ultimate sin, but it's really not as bad as it sounds. First of all, you're not really snitching on anyone. Instead, you are trying to convince the system administrator (via dice rolls) that he has hackers on his system. If you are successful, then the administrator will initiate a housecleaning in an attempt to rid the system of hackers. Like hacking and phreaking, narking has its dangers, not the least of which is getting everyone else pissed off at you.
By now, you probably realize that Hacker is not an easy game to play without the rule book handy. Indeed, we found the rules to be in such high demand that we made extra copies. While it's not really complicated, it does take some time to learn. The best way to describe Hacker is that it is interesting and entertaining. Members of 2600 played it for seven straight hours, and only stopped due to severe exhaustion. In some ways, the game has more in common with real hacking then you might think!
Hacker will not teach you how to hack. Obviously no game is a substitute for the real thing. However, Hacker may help explain some of the fundamental concepts of its namesake by letting people vicariously experience the thrill of true hacking. The terms used in the game are fairly accurate. The only term we had a problem with was "phreaking." In reality, phreaking has very little to do with allowing fellow hackers a shot at an account on a system that you already have access to.
Hacker manages to capture the spirit of hacking in a cardboard box. True to its name, the main goal is not to invade privacy, or increase one's wealth, or cause anarchy. Rather, the goal is merely to gain access, to explore, and to have fun while doing it. Jackson's use of a network connecting government and corporate systems is noteworthy. Obviously, you will not find Mom and Pop's home computer on the Internet. Perhaps this will help dispel the myth that hackers invade "personal" privacy.
Even creativity, that most important of all aspects of hacking, is present in the game. The rule book is by no means definitive, and players will find creative ways to bend, twist, and distort various sections to produce tangible results. For instance, the rules do not say anything about getting more than one account on a system. However, what is ultimately "allowed" and "prohibited" will be determined by the players On more than one occasion, we found ourselves voting on controversial rule-book ambiguities. Law enforcement officials will therefore be pleased to know that Hacker, among other things, encourages democracy.