Date: Fri, 06 Jan 2012 17:00:07 -0500
From: "James M. Atkinson" <jm...@tscm.com>
Organization: Granite Island Group
Subject: Re: [TSCM-L] {5986} POTUS telephones
Most of these are CISCO IP phones, or Avaya telephone sets.
Amazing complex instrument with some simply lovely security holes that
an eavesdropper can exploit.
http://www.cisco.com/en/US/products/ps9748/index.html
http://www.cisco.com/en/US/products/ps8538/index.html
http://www.cisco.com/en/US/products/hw/phones/ps379/ps5440/index.html
http://www.cisco.com/en/US/products/hw/phones/ps379/index.html
A lot of these phones are also Lucent MLS of Definite phones (all an
eavesdroppers paradise).
I really hate to have to mention this, but in the followign image:
 You will notice the moron who is using a cell phone right next to a STE
Same here:
You will notice the moron who is using a cell phone right next to a STE
Same here: 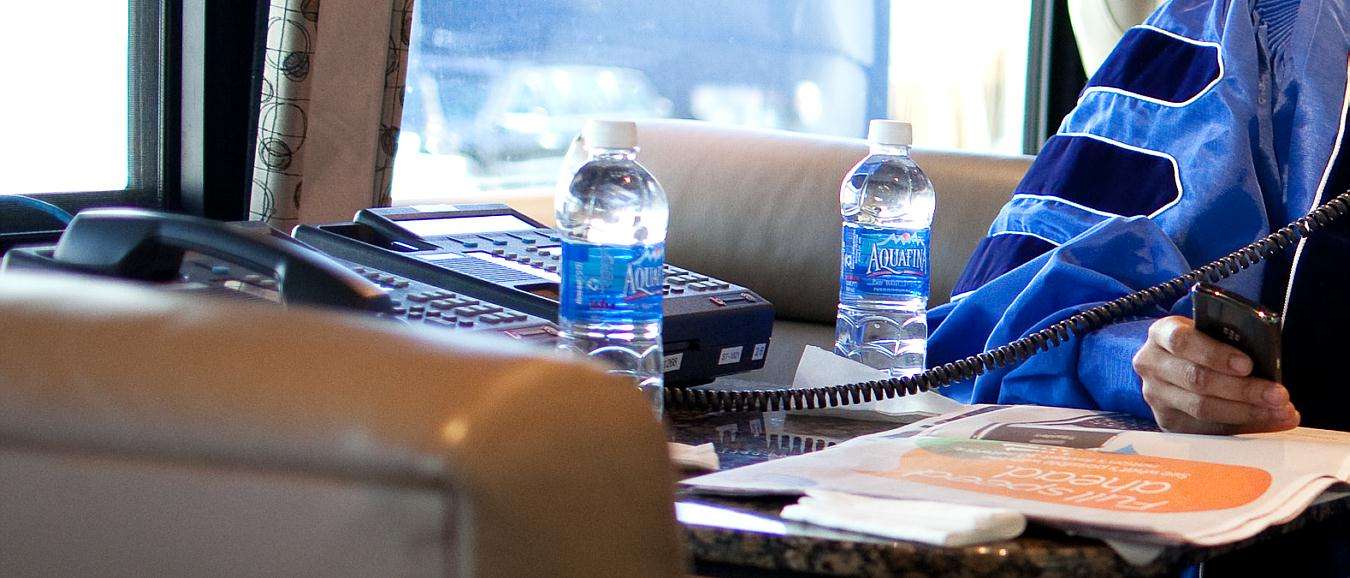 Moron using cell phone in close proximity to a secure telephone.
When you place a concentrated RF signal transmitter in close proximity
to a piece of cryptographic gear (like a STU or STE) the RF signals and
strong enough to intermix with the RF or magnetic signals and create a
third signal. This is most valuable with cryptographic equipment that
used cables that was not in conduit as the cable (seem in these
pictures) provides a high threat access point where all kinds of havoc
can be caused if a cell phone is brought within 8-12 feet of a STU, or
16+ feet of a STE. You will notice that the moron holding the phone is
well within those distances.
The following image just proved what a utter moron this guy is, and
remember who is is:
Moron using cell phone in close proximity to a secure telephone.
When you place a concentrated RF signal transmitter in close proximity
to a piece of cryptographic gear (like a STU or STE) the RF signals and
strong enough to intermix with the RF or magnetic signals and create a
third signal. This is most valuable with cryptographic equipment that
used cables that was not in conduit as the cable (seem in these
pictures) provides a high threat access point where all kinds of havoc
can be caused if a cell phone is brought within 8-12 feet of a STU, or
16+ feet of a STE. You will notice that the moron holding the phone is
well within those distances.
The following image just proved what a utter moron this guy is, and
remember who is is: 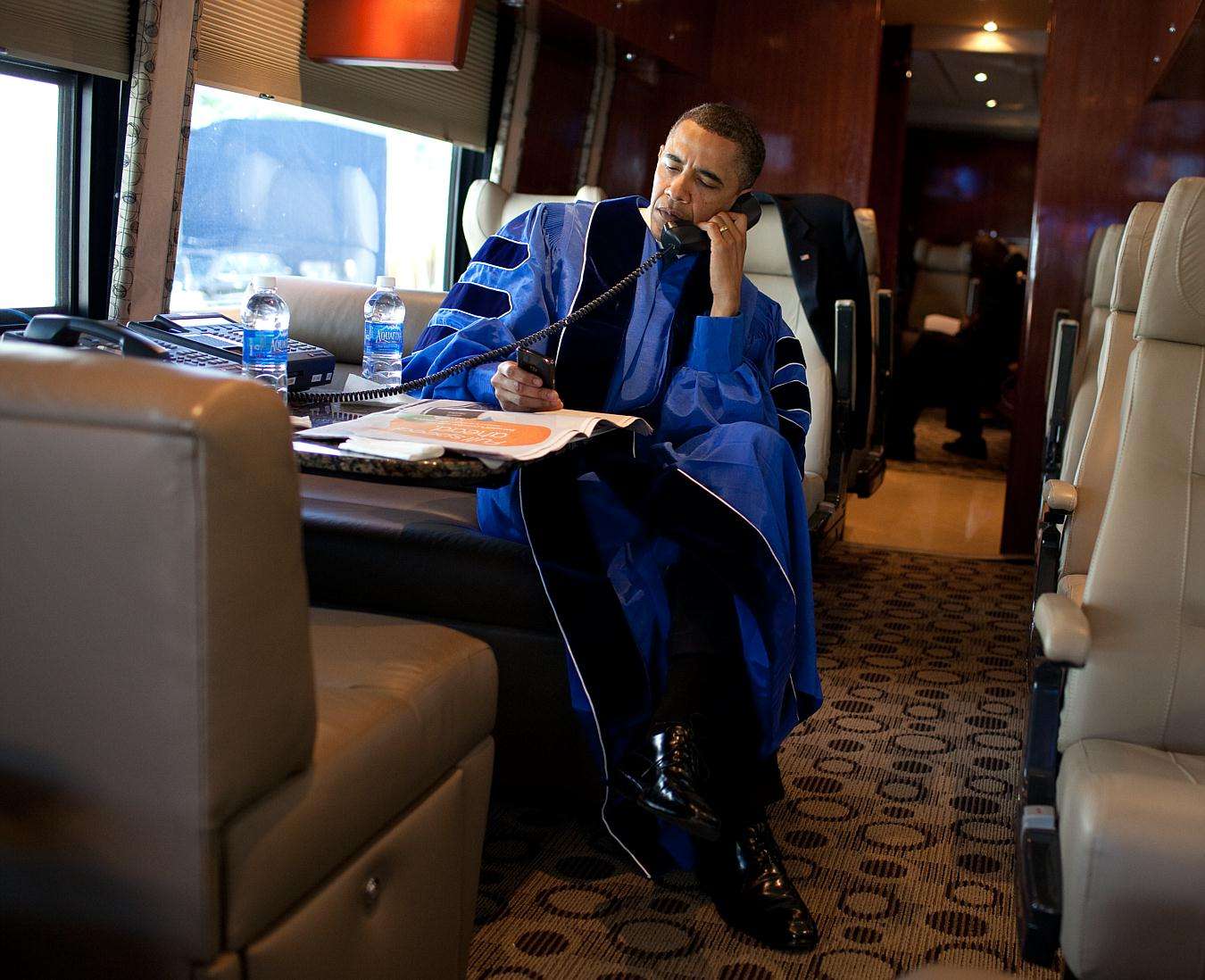 Notice that he is in a STE, in secure mode, and the STE (unencrypted
voice path) is draped over a live RF transmitter.
I apologize Mr. President, but you sir are a fscking moron, just an
utter moron.
Observers with sharp eyes will also notice the profoundly sloppy jobs of
TSCM that is being done on these phones as well, and how the routing
requirements for cables are not beign observered, but then that is the
least of thier probelms... thier boss obviously does not care, so why
shoudl they.
Dude, WTF... no seriously, WTF?
-jma
Notice that he is in a STE, in secure mode, and the STE (unencrypted
voice path) is draped over a live RF transmitter.
I apologize Mr. President, but you sir are a fscking moron, just an
utter moron.
Observers with sharp eyes will also notice the profoundly sloppy jobs of
TSCM that is being done on these phones as well, and how the routing
requirements for cables are not beign observered, but then that is the
least of thier probelms... thier boss obviously does not care, so why
shoudl they.
Dude, WTF... no seriously, WTF?
-jma
Date: Fri, 06 Jan 2012 18:19:17 -0500
From: "James M. Atkinson" <jm...@tscm.com>
Reply-To: tscm-l2006@googlegroups.com
Organization: Granite Island Group
Subject: Re: [TSCM-L] {5989} POTUS telephones
Actually yes.
He knows that he can not use a cellphone within X feet of a STU, STE, or
security communications media because he can read the white papers on
the matter, and has been briefed by the technical advisors until they
were blue in the face, but he does not care, he likes his cell phones
(because it makes him a more effective leader)
If a customer hires me to tell them about the problem, and I tell them
about it, write numerous white papers on the subject for them,
demonstrate the risk for them by recovering classified information, and
even the CIK form a STU using only a nearby cell phone, and they still
refuse to use proper communications security, and abide by stand-off
distances (the space between the secure phone and the cell phone), then
I will have no problems explain that they are a moron to their face
(usually in private, but still).
You need only to watch the video of my testimony before Congress on
related matters to see that I tend not to couch my words when it comes
to national security matters like this.
The President of the United States is a f*cking moron, but given the
last pool of candidates he is less of a moron, then the other morons we
had running at the time. But still, he is a moron, and an arrogant one
at that.
-jma
bernieS wrote:
> Are executives at the highest levels expected to be TSCM, COMSEC, and
> TEMPEST experts who possess detailed technical knowledge and extensive
> related experience?
>
> If yes, then why would any top executive have any need to hire experts
> in those fields? Does JMA call his executive clients (who aren't as
> well-versed in those fields as he obviously is) "f*cking morons?"
> That doesn't seem like an effective business practice to me.
>
> Perhaps the executive in the photo wasn't briefed by his experts on
> the finer points of proper COMSEC--such as not to use a cell phone
> near a STE. If he wasn't, then perhaps those experts are to blame,
> not the executive. Or maybe there's other protections in place which
> prevent that from being a COMSEC problem. There is equipment in those
> photos that probably none of us know the workings of...
Date: Fri, 06 Jan 2012 19:17:28 -0500
From: "James M. Atkinson" <jm...@tscm.com>
Reply-To: tscm-l2006@googlegroups.com
Organization: Granite Island Group
Subject: Re: [TSCM-L] {5992} POTUS telephones
I wrote the white paper, and the paper has been repeatedly briefed to
him by the DCI in his Daily Presidential Briefing. He has also read the
white paper, but it has not dissuaded his cell phone mis-use. Several
DCI staffers who prepare the PDB have assured me that the DCI has
repeatedly included issue several times in the PDB, and POTUS just does
not care.
The threat is known, the threat has been demonstrated, the threat has
been replicated by others, it is a known and confirmed weakness, but he
does not care, not even slightly.
Some Presidents like to ride around Dallas in open top limos, other are
addicted to their cell phones... neither tend to remain in office too long.
He needs to smarten up, as he is risking national security and
sabotaging international diplomacy (easily screwed up when secure
communications are intercepted).
-jma
bernieS wrote:
> At 06:19 PM 1/6/2012, JMA wrote:
>> Actually yes.
>>
>> He knows that he can not use a cellphone within X feet of a STU, STE,
>> or security communications media because he can read the white papers
>> on the matter, and has been briefed by the technical advisors until
> they were blue in the face, but he does not care, he likes his cell
>> phones (because it makes him a more effective leader)
>
> So you know this for a fact? I would think POTUS has more important
> things to do than "read the white papers" about TSCM. Arrogant?
> Relative to whom?
Date: Tue, 10 Jan 2012 17:00:07 -0500
From: "James M. Atkinson" <jm...@tscm.com>
Organization: Granite Island Group
Subject: Re: [TSCM-L] {6009} Re: {5984} POTUS telephones
The most dramatic of all vulnerabilities is the sidetone audio on the
STU and STE handsets, and this is an amplified audio signal, and the
handset cord lacks magnetic shielding, so the magnetic energy of the
AMPLIFIED handset audio presents a modestly strong magnetic field around
the handset cord. While this magnetic field does drop off at a rapid
rate, any sort of radio frequency (RF) emitting device that generate an
RF signal that is stronger then around -80 dBm allows allows the audio
that is present on the handset cord to be intercepted a considerable
distance away as it actually modulates or is carried on the back of the
RF signal (in this case form a cell telephone).
If does not matter what kind of a sell phone it is, or if it is a
"secure" cell phone of not, merely because it creates an intense RF
field, and then that field is in close proximity to the handset of a STU
or STE means that the audio on the phone (not get encrypted or scrambled
audio) can be eavesdropped upon at distance well in excess of 1200 feet.
An typical iPhone or Blackberry, and a typical STU or STE when brought
in close proximity to one another renders the security moot due to the
audio riding on the back of the RF. It does not matter how well the
phone itself is shield or not shielded the initial vulnerability to this
is in the handset and the handset cord. This is the "elephant in the
room" as it were, and it provides the most dramatic results on a
demonstration of this vulnerability.
Next is the power supply of the STU-III and the power cord of the STE.
The STU-III was the subject of a study that was pretty ugly, and when
the study was published and the U.S. Government started check the
STU-III Power Supplies a great number were discovered to have extra
electronics. The phone itself was not targeted, it was the power supply.
Foreign intelligence agencies for years exploits the modular nature of
the STU-III power supply, and the handsets to inject compromised power
supplies and handsets into the distribution chain, and into field units.
The STE's also have a very nasty vulnerability in regards to the power
cords as they require and ultra-clean ground, and the shielding of the
STE can be render useless when the power cord gets bend of "piggy
tailed" as you can see in these images. The power cord can not be formed
into a loop that is less then 8 inches in diameter, or the phones will
leak more then a 60 year old porn star. A STE with a "piggy tailed"
power cord also indicated that the President has a spy doing stuff to
his phones as this is a prime visual indicator of tampering, and power
cord needs to be impounded and fingerprints lifted to see who did it.
The STE also has to have both the power cord and the phone cord exit the
phone straight for about a foot, and the phone cable absolutely can not
be passed under the phone, and most especially not along the right side
of the phone. This is a major COMSEC violation.
When these phones have the internal key generator active then a cell
phone has to be kept well outside the stand off ranges, or you WILL
piggy back enough of the key so they it can be rebuild it in complete
form in a matter of mere milliseconds. The stronger the source, or the
longer the duration of the phone transmission the more of the internal
cipher stages are disclosed. Much of the key of worthless, but the core
of what is used to set up the key generator into its initial stages, and
then to form the loops within the cipher. These are the most holy
secrets of any ciphering system, and it is what a spy will spend great
effort to obtain. The STU-III has several notable "leak points" as does
the "STE" but these are a known and limit problems until some fool
brings a cell phone or PDA close to the STU or STE.
There is magnetic shielding, and then electrical shielding, and each
have issues on each product and known and documented holes.
The KOV-14 is vulnerable to RF illumination between 700 and 2.6 GHz and
live data can be received from the cards when they are in operation
merely by proximity to an operations cell phone. GSM standards provide
the best illumination sources of a KOV-14.
-jma
Joe Tag wrote:
> I have a comment and question: The cellphone seems to be a Sectera phone
> (Motorola TimePort with secure slice/wedge). Doesn't the Sectera have
> shielding painted in? Isn't the STE in an aluminum case (and the handset
> low voltage)? How serious is the EMF issue?
>
> I do agree with the later Blackberry PDA phone however.
>
> The General Dynamics (GD) SME-PED phone is shielded, and has crypto
> comparable to Sectera i believe. Also, L3-Communications (maker of
> the STE phone; that phone uses a Krypton KOV-14 card) also makes and
> sells a SME-PED phone (also shielded, I believe) to compete with GD.
> If I am wrong, please correct me.
>
> Thanks, Jim.
Undo Arduino Encryption With An Oscilloscope
 You will notice the moron who is using a cell phone right next to a STE
Same here:
You will notice the moron who is using a cell phone right next to a STE
Same here: 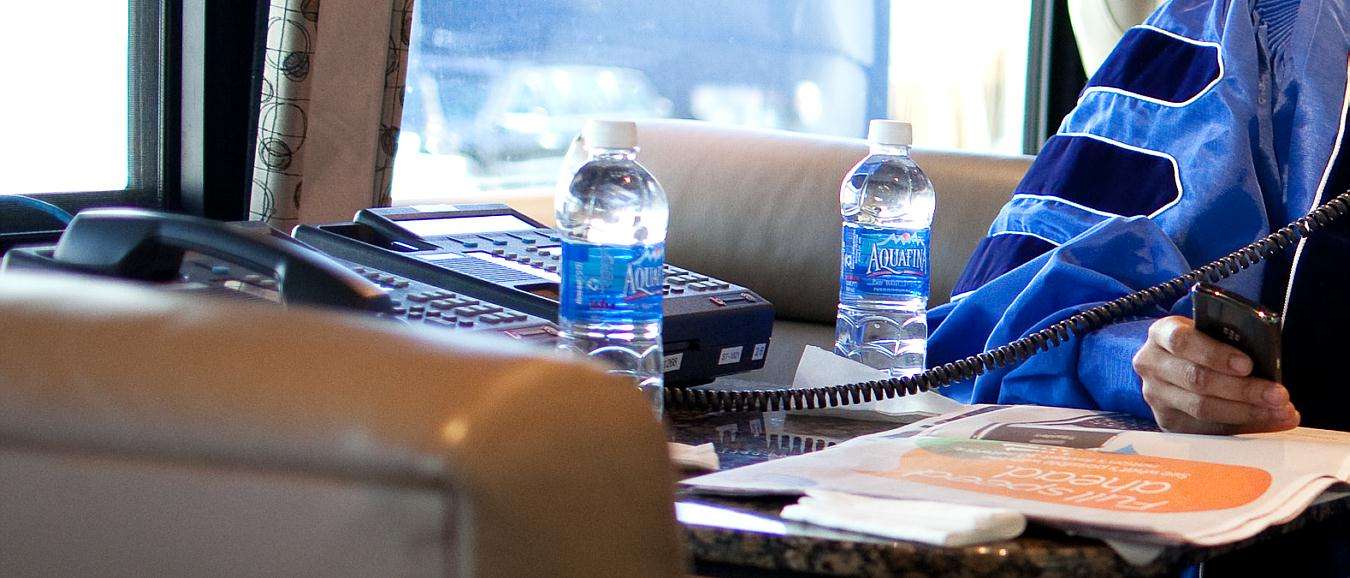 Moron using cell phone in close proximity to a secure telephone.
When you place a concentrated RF signal transmitter in close proximity
to a piece of cryptographic gear (like a STU or STE) the RF signals and
strong enough to intermix with the RF or magnetic signals and create a
third signal. This is most valuable with cryptographic equipment that
used cables that was not in conduit as the cable (seem in these
pictures) provides a high threat access point where all kinds of havoc
can be caused if a cell phone is brought within 8-12 feet of a STU, or
16+ feet of a STE. You will notice that the moron holding the phone is
well within those distances.
The following image just proved what a utter moron this guy is, and
remember who is is:
Moron using cell phone in close proximity to a secure telephone.
When you place a concentrated RF signal transmitter in close proximity
to a piece of cryptographic gear (like a STU or STE) the RF signals and
strong enough to intermix with the RF or magnetic signals and create a
third signal. This is most valuable with cryptographic equipment that
used cables that was not in conduit as the cable (seem in these
pictures) provides a high threat access point where all kinds of havoc
can be caused if a cell phone is brought within 8-12 feet of a STU, or
16+ feet of a STE. You will notice that the moron holding the phone is
well within those distances.
The following image just proved what a utter moron this guy is, and
remember who is is: 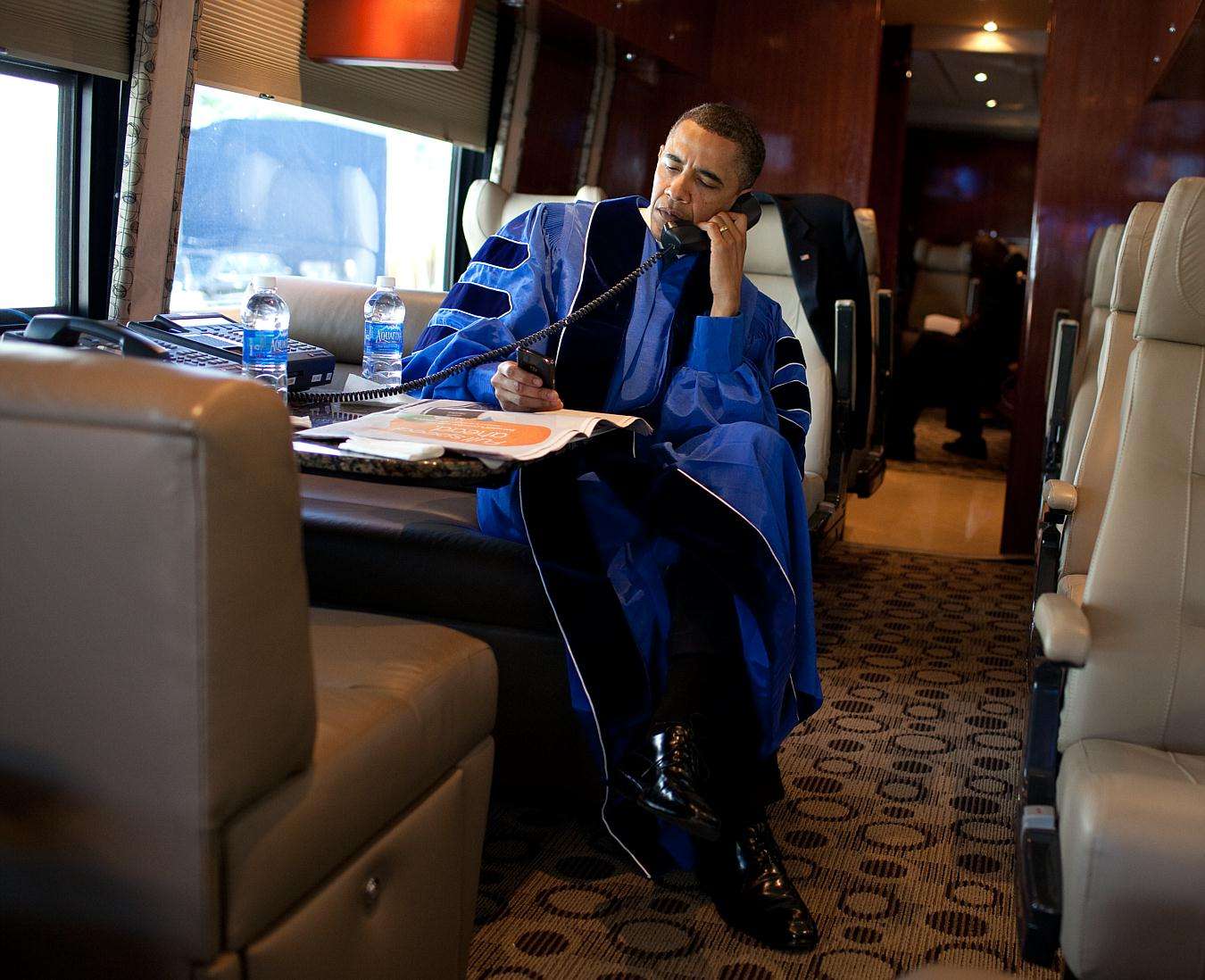 Notice that he is in a STE, in secure mode, and the STE (unencrypted
voice path) is draped over a live RF transmitter.
I apologize Mr. President, but you sir are a fscking moron, just an
utter moron.
Observers with sharp eyes will also notice the profoundly sloppy jobs of
TSCM that is being done on these phones as well, and how the routing
requirements for cables are not beign observered, but then that is the
least of thier probelms... thier boss obviously does not care, so why
shoudl they.
Dude, WTF... no seriously, WTF?
-jma
Notice that he is in a STE, in secure mode, and the STE (unencrypted
voice path) is draped over a live RF transmitter.
I apologize Mr. President, but you sir are a fscking moron, just an
utter moron.
Observers with sharp eyes will also notice the profoundly sloppy jobs of
TSCM that is being done on these phones as well, and how the routing
requirements for cables are not beign observered, but then that is the
least of thier probelms... thier boss obviously does not care, so why
shoudl they.
Dude, WTF... no seriously, WTF?
-jma